Botnet trap IoT: Why verifiable identities are crucial. A practical example
What used to be a niche problem now affects a wide range of IoT devices, like smart speakers, surveillance cameras, industrial control systems, routers, medical devices and even vehicle components. The good news: The risk of botnet attacks can be drastically reduced with verifiable, decentralised identities. We’ll show how this works here!
IoT devices as silent gateways for attackers
The number of connected devices is growing rapidly – and with it the risk of falling victim to an IoT botnet attack. What used to be a niche problem now affects smart speakers, surveillance cameras, industrial control systems, routers, medical devices and even vehicle components.
Precisely because IoT devices often appear inconspicuous, they become silent gateways for attackers. A compromised device then works unnoticed in a botnet – and can become part of massive cyber attacks that paralyse entire companies or even parts of the internet.
But there is good news:
This risk can be drastically reduced with verifiable, decentralised identities.
How does this work? We’ll show you here.
IoT botnets:
The underestimated threat
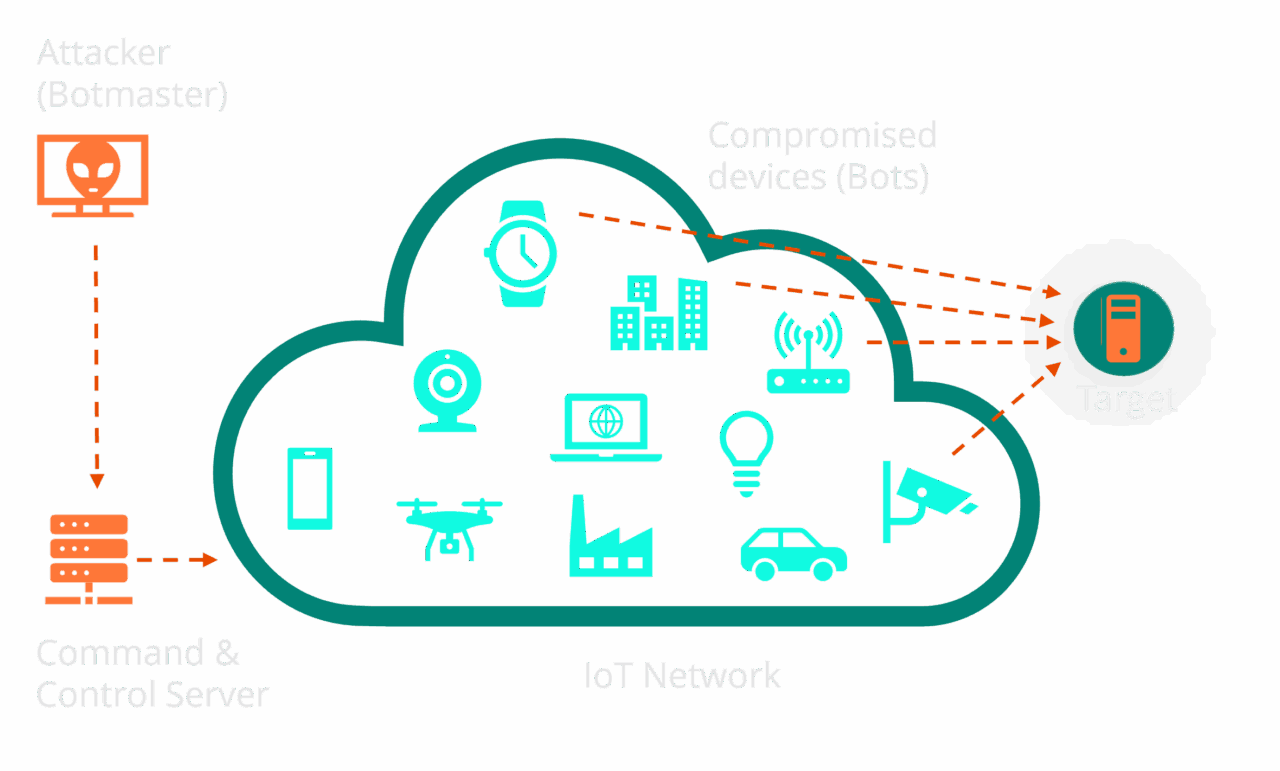
An IoT botnet consists of compromised devices that are under the control of an attacker. These devices appear completely normal to the outside world, but execute commands in the background – whether DDoS attacks, cryptomining, spreading malware or manipulating critical data.
One of the most well-known cases is Mirai. Originally created “by accident” by three developers, the Mirai botnet paralysed large parts of the internet in 2016 – including major platforms such as Twitter, LinkedIn and entire banking environments. The subsequent release of the source code – a deliberate strategy to conceal its origin – continues to this day to ensure that new variants keep emerging.
Since 2024, security researchers have also observed a significant increase in such botnet activity – increasingly professional, partly state-organised and technically sophisticated.
Why IoT devices are particularly affected
Many IoT devices are vulnerable because:
- Standard passwords are not changed
- Updates are missing or not even planned
- Weak or outdated cryptographic methods are used
- Manufacturers of inexpensive consumer devices place little emphasis on security
- Users themselves have no IT expertise
The result:
A botnet can spread quickly, quietly and decentrally – and cause enormous damage. In addition to production downtime and IT outages, manufacturers who fail to meet CRA or RED requirements will also face heavy penalties in future.
Zero Trust for IoT – Identities instead of passwords
The key question is:
How can I ensure that every device is unique – and only does what it is allowed to do?
The answer:
Verifiable, decentralised identities (DID & VC).
Instead of passwords or mountains of certificates, modern IoT systems will in future work with cryptographically secured identities that:
- cannot be guessed
- cannot be compromised via central servers
- contain forgery-proof attributes
- can be managed throughout their entire life cycle
This principle is not new – the EU is currently introducing digital citizenship (EUDI Wallet) based on the same standards. And it is precisely these technologies that we at filancore are bringing to the IoT world.
How do verifiable identities work in the IoT?
Each device is assigned a unique digital identity during production. Manufacturers can issue cryptographically signed authorisations, e.g.:
- Who is permitted to configure the device?
- Where is it permitted to connect?
- From whom is it permitted to receive updates?
- What data is it permitted to send?

This allows a device to check at any time:
- Who is giving him instructions
- Whether this person or machine is authorised
- Whether manipulated software is to be installed
The result:
no passwords, no certificate hell – instead, zero trust at device level.
A practical example:
secure smart care products
A partner company in the healthcare sector develops smart home devices for people in need of care. These devices must be particularly safe, as they enable, among other things:
- Video communication with carers
- Opening smart doors
- Vital notifications
- Remote access for service personnel
The problem: many users are not IT-savvy. Passwords or complex update processes would be a security risk – and simply not practical.

Filancore solved the following issues:
✔ Easy to use
Devices can be put into operation via QR code or automatically – without any technical hurdles for nursing staff or relatives.
✔ Ownership
Sensitive data remains transparent to the owner, who decides on its availability and disclosure.
✔ Easy integration & onboarding
Third parties and service providers can be seamlessly added and granted access to relevant data on a need-to-know basis.
✔ Passwordless authentication
Each device has a strong cryptographic identity. Only those with the appropriate authorisation can access it – without any passwords.
✔ Cost savings compared to PKI
Since no traditional certificate PKI is required, infrastructure and maintenance costs are significantly reduced – often by a factor of 5–10.
✔ Tamper-proof over-the-air updates
Updates are only accepted if they have been cryptographically verified by the manufacturer. This means that a botnet cannot install a manipulated update.
✔ Protection against botnet takeover
Without passwords and with secure update processes, the risk of compromise is drastically reduced.
Why verifiable identities are becoming the new standard
The increasing threat situation, new EU regulations and growing complexity in the IoT lead to one clear conclusion: Without verifiable identities, IoT devices can no longer be operated securely in the long term.
Decentralised identities create an ecosystem in which every device is:
- Uniquely identifiable
- Verifiable at any time
- Cryptographically securedTamper-resistant
- Compliant with standards
– completely without central single points of failure.
Conclusion: IoT security begins with identity
IoT botnets are not a hypothetical risk, but a reality. However, the solution is just as real: verifiable identities create the basis for zero-trust security in the IoT – simple, scalable and future-proof.
filancore supports manufacturers in using these technologies without complex integration hurdles – from the initial device identity to global rollout.
How is your IoT security
Request your free quick check
If you would like to know how well your current IoT security architecture is positioned, we recommend our IoT Security Quick Check – free of charge and without obligation. Just contact us via the email form below: